Blockchains are very popular now.
As the name suggests, blockchain is a chain of blocks. When we say the words “block” and “chain” in this context, we talk about digital information (“block”) stored in a public database (“chain”).
A blockchain is a distributed entry, that is accessible to anyone. To any data recorded inside a blockchain, any modifications are challenging in keeping a blockchain functional.
Keep in mind!

- Blockchain is not Bitcoin, but it is the technology behind Bitcoin;
- Bitcoin is the digital token and blockchain is the ledger to keep track of who owns the digital tokens;
- You can’t have Bitcoin without blockchain, but you can have a blockchain without Bitcoin.
Blockchain architecture
Well, let’s take a look at the block content.

Each block consists of:
- some data;
- hash of the current block;
- hash of the previous block.
The data stored inside a block depends on the type of the blockchain. For example, a bitcoin blockchain stocks in the block the details about the transaction.

The hash inside the block is unique, and it identifies the block and all of its contents. Once a block is formed, in no time, its hash mapped. The modifications inside the block data transform the hash.

The third element is the hash of the previous block in the chain. And this, effectively, creates a chain of blocks. Got it? If yes, then you got the technique that makes the blockchain so secure.
Let’s look at an example.
Imagine a chain of 3 blocks:

The first block in the chain – called the Genesis block – without a predecessor. Block 2 contains the hash of block 1, while block 3 contains the hash of block 2.
Imagine a hacker can change the existing data in Block 2. Now, his action triggers the change in the hash of the block. But, because Block 3 still contains the old hash of Block 2, those changes make Block 3, and all succeeding blocks invalid because they do not have the exact hash of the previous block.
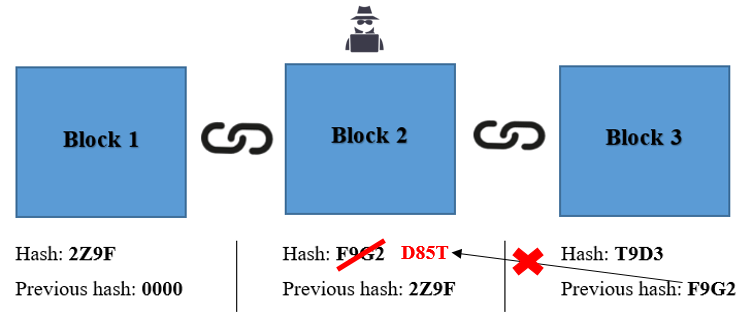
So, changing a single block will make the rest of the following blocks invalid.
But is this enough to secure a blockchain?
No, using hashes is not enough to prevent tampering. Nowadays, computers are very fast and can calculate 100 000 of hashes per second. So, you can tamper a block and recalculate all the hashes of other blocks, and it makes the blockchain valid again. There are two more steps needed to ensure the blockchain and avoid such situations.
I. Blockchain has a specific mechanism called Proof-of-work. It is a mechanism that slows down the creation of new blocks. In bitcoin’s case, it takes about 10 minutes to calculate the required proof-of-work and add a new block to the chain. This mechanism makes it very hard to attack the blocks – if you tamper one block, you need to recalculate proof-of-work for all the following blocks. So, the security of the blockchain comes from creating the hashes and the proof-of-work mechanism.
II. Instead of using a central entity to control the chain, a blockchain uses a P2P network, where individual members are entitled to participate. When someone enters the system, he also acquires a full copy of the blockchain and verifies if everything is in order.

When any user creates a new block, it is sent to all the users in the network. Each node has to verify and make sure there was no alteration. After a complete check, each node adds this block to its blockchain.
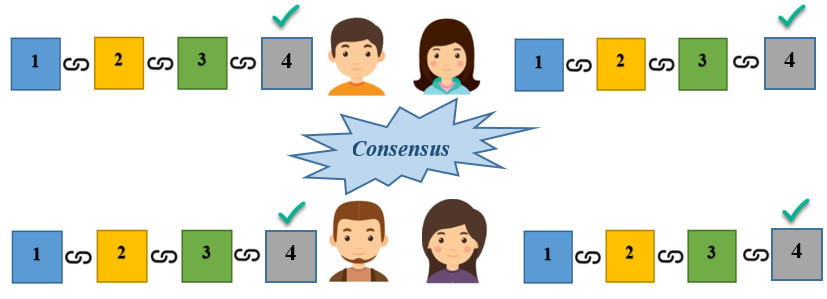
The nodes in the network create a consensus that recognizes the blocks that are or aren’t valid and rejects the tampered ones.
Now, to successfully tamper with a blockchain, you need to:
- Tamper with all the blocks in the chain;
- Redo the proof-of-work for each block;
- Take control of higher than 50% of the peer-to-peer network.
Your tampered block becomes accepted by everyone else, only by following these steps, but this seems to be an impossible task because the Blockchains are secured.
What’s a Blockchain Transaction?

Step 1. A person requests a transaction of cryptocurrency, contracts, records, or other information.
Step 2. The request is broadcasted to a P2P network with the help of nodes.
Step 3. The network of nodes validates the transaction and the user’s status with the help of known algorithms.
Step 4. After the complete transaction, it becomes permanent and unalterable, and the new block added to the existing blockchain.
Where is the Blockchain technology applied?
The blockchain technology is used in different sectors – the table below shows an example. These are some of the examples of how blockchains use more divisions and with more practice cases.
| Sector | Usage |
|---|---|
| Markets | Billing, monitoring and Data Transfer |
| Government Sector |
|
| IoT |
|
| Finance & Accounting |
|
You just learned something new about blockchains. See you soon for more!

